 Your new post is loading...
 Your new post is loading...
Um die Schüler auf die Arbeitsplätze von morgen optimal vorzubereiten, muss die Schule sich der modernen Informations- und Kommunikationstechnologien bedienen. Am Mittwoch stellte Bildungsminister Claude Meisch die Strategie "Digital (4) Education" vor, mit der die Schüler von heute, deren Lebenswirklichkeit bereits in weiten Teilen eine digitale ist, auf morgen vorbereitet werden sollen.
Via Gust MEES
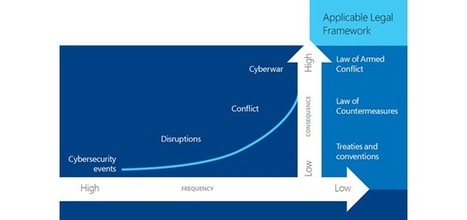
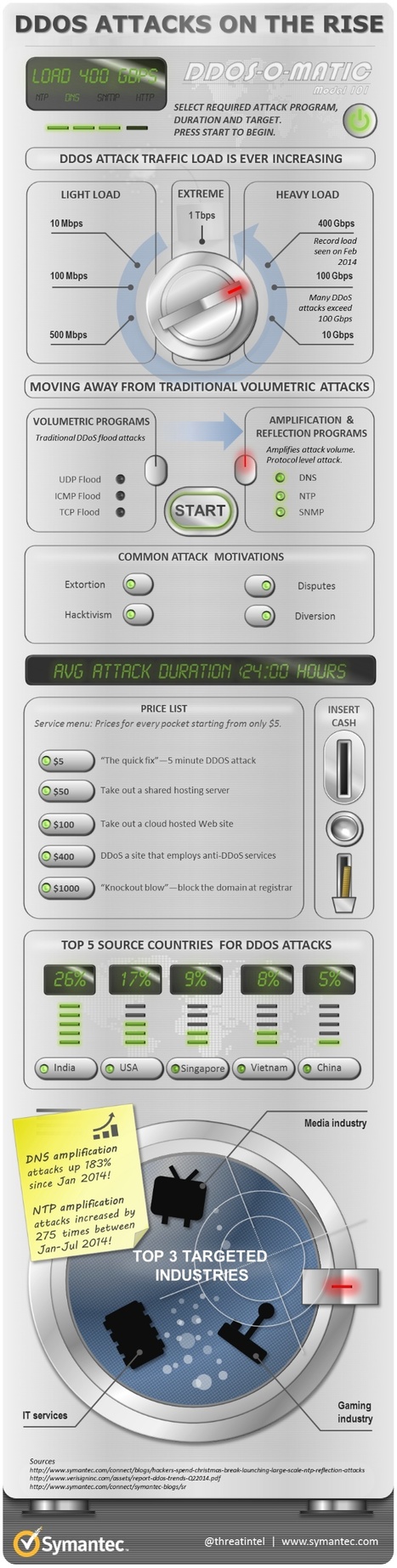
The Internet has by and large been a cause for good, driving economic growth across developed and emerging economies, connecting individuals and communities to previously unattainable services, and propelling innovation online, as well as offline. Today, all over the world public utilities, banks, and governments use the Internet, cloud services, and mobile technology to enhance their productivity. Unfortunately, the benefits of greater connectivity have also brought about increased information
Via Gust MEES
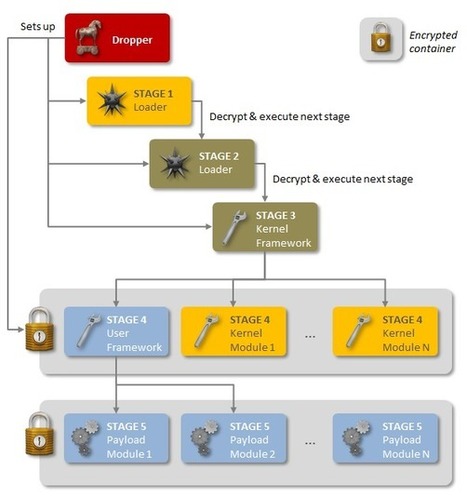
An advanced piece of malware, known as Regin, has been used in systematic spying campaigns against a range of international targets since at least 2008. A back door-type Trojan, Regin is a complex piece of malware whose structure displays a degree of technical competence rarely seen. Customizable with an extensive range of capabilities depending on the target, it provides its controllers with a powerful framework for mass surveillance and has been used in spying operations against government organizations, infrastructure operators, businesses, researchers, and private individuals.
It is likely that its development took months, if not years, to complete and its authors have gone to great lengths to cover its tracks. Its capabilities and the level of resources behind Regin indicate that it is one of the main cyberespionage tools used by a nation state.
As outlined in a new technical whitepaper from Symantec, Backdoor.Regin is a multi-staged threat and each stage is hidden and encrypted, with the exception of the first stage. Executing the first stage starts a domino chain of decryption and loading of each subsequent stage for a total of five stages. Each individual stage provides little information on the complete package. Only by acquiring all five stages is it possible to analyze and understand the threat.
Via Gust MEES
DOS ATTACKS ON THE RISE | Cyber Security | Infographic
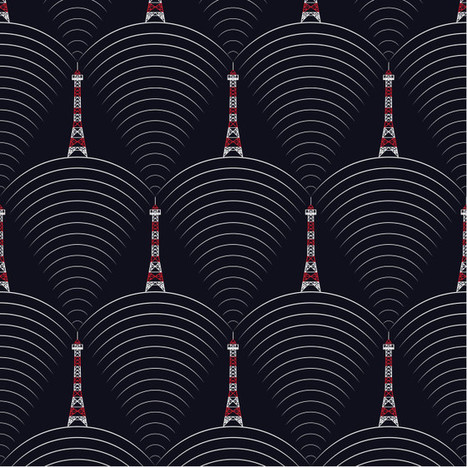
Dubbed “AirHopper” by the researchers at Cyber Security Labs at Ben Gurion University, the proof-of-concept technique allows hackers and spies to surreptitiously siphon passwords and other data from an infected computer using radio signals generated and transmitted by the computer and received by a mobile phone. The research was conducted by Mordechai Guri, Gabi Kedma, Assaf Kachlon, and overseen by their advisor Yuval Elovici.
The attack borrows in part from previous research showing how radio signals (.pdf) can be generated by a computer’s video card (.pdf). The researchers in Israel have developed malware that exploits this vulnerability by generating radio signals that can transmit modulated data that is then received and decoded by the FM radio receiver built into mobile phones. FM receivers come installed in many mobile phones as an emergency backup, in part, for receiving radio transmissions when the internet and cell networks are down. Using this function, however, attackers can turn a ubiquitous and seemingly innocuous device into an ingenious spy tool. Though a company or agency may think it has protected its air-gapped network by detaching it from the outside world, the mobile phones on employee desktops and in their pockets still provide attackers with a vector to reach classified and other sensitive data.
Via Gust MEES
L’ENISA fête cette année ses 10 ans au service de la cyber-sécurité. C’était également l’occasion d’ouvrir le Mois européen de la cyber-sécurité.
Impliquer le citoyen était au cœur du débat mené par François Thill, responsable CASES, membre du conseil d’administration de l’ENISA et coordinateur des activités ECSM pour le Luxembourg.
Le Luxembourg est l’un des pays pilotes en Europe quant à la sensibilisation grand public aux bonnes pratiques des technologies de l’information. Les initiatives telles que CASES, CIRCL et BEE SECURE ont commencé à émerger au Grand-Duché il y a une bonne dizaine d’années déjà. Elles sont aujourd’hui coordonnées par « Security made in Lëtzebuerg » (SMILE), le groupement d'intérêt économique qui a été mandaté en 2010 par le ministère de l'Economie pour renforcer la sécurité de l'information au Grand-Duché de Luxembourg. CASES, CIRCL et BEE SECURE ont pour mission de développer le niveau de savoir-faire de la population en matière d’Internet, en démocratisant les informations, les méthodes et les connaissances existantes. Leur objectif ultime est de faire bénéficier les utilisateurs des opportunités que livre l’Internet dans un climat de confiance et de résilience par rapport aux risques.
Via Gust MEES
F-Secure Security Labs brings you the latest online security news from around the world. Ensure that you are up-to-date with the latest online threats to guarantee your online wellbeing.
Via Gust MEES
Proactive THINKing MUST be part Of EDUcation Responsibility While Using ICT
|
The Internet of Everything (IoE) represents the next “world-changing” revolution, after the Industrial Revolution of 1750 – 1900, and following the Computer & Internet revolution which started in the 1950’s. It is an exciting scenario in which objects, personal devices, even animals communicate, take Intelligent decisions, and autonomous actions on their own without human interaction. This revolution will completely transform industrial sectors and the entire world, for all of us, in ways as powerful as the Industrial Revolution and even more. It is our future, and it is happening now.
How is it happening? For an Evolution of Technologies, and with a Revolution of Minds… Learn more: - http://www.scoop.it/t/securite-pc-et-internet/?tag=smart-TV - http://www.scoop.it/t/21st-century-learning-and-teaching/?tag=Internet+of+Things - http://www.scoop.it/t/securite-pc-et-internet/?tag=Internet+of+things - http://globaleducationandsocialmedia.wordpress.com/2014/01/21/why-is-it-a-must-to-have-basics-knowledge-of-cyber-security-in-a-connected-technology-world/
Via Gust MEES, Lynnette Van Dyke
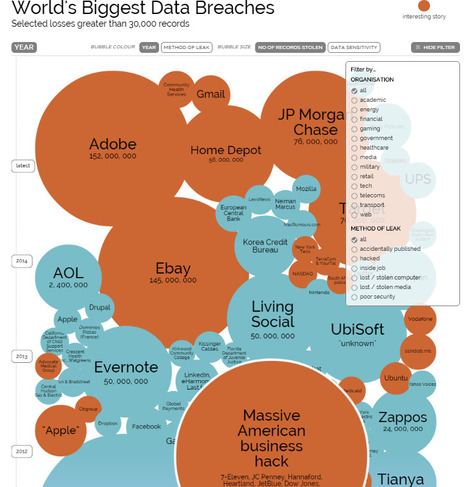
The 27001 Academy has produced an informative infographic that illustrates key details of the nearly 800 reported data breaches in the U.S. that occurred in 2014 - up about 20% from 2013.
Surprisingly, despite the sharp increase in the number of breaches seen last year, the actual number of records that were compromised was down more than
Learn more:
- http://www.scoop.it/t/securite-pc-et-internet/?tag=DATA-BREACHES
Via Gust MEES
How many of these hacker personas are you dueling with in your organization?
Via Gust MEES, Next Level
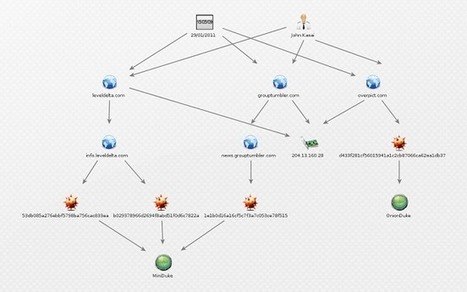
Recently, research was published identifying a Tor exit node, located in Russia, that was consistently and maliciously modifying any uncompressed Windows executables downloaded through it. Naturally this piqued our interest, so we decided to peer down the rabbit hole. Suffice to say, the hole was a lot deeper than we expected! In fact, it went all the way back to the notorious Russian APT family MiniDuke, known to have been used in targeted attacks against NATO and European government agencies.
The malware used in this case is, however, not a version of MiniDuke. It is instead a separate, distinct family of malware that we have since taken to calling OnionDuke.
Learn more:
- http://www.scoop.it/t/securite-pc-et-internet/?tag=TOR
Via Gust MEES
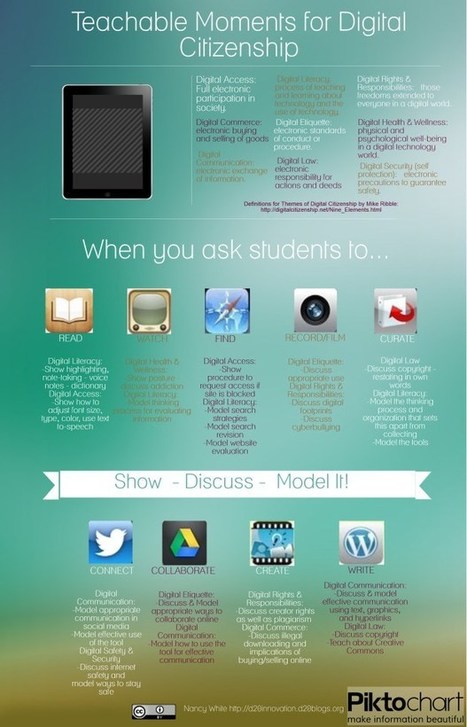
Learning To Become a GOOD Digital Citizen | Digital CitizenShip | How To? Well, there is a lot of different views! WE will explore WHAT could be THE BEST way to teach and to learn about Digital...
Via Gust MEES, Next Level
|



 Your new post is loading...
Your new post is loading...












![H1 2014 Threat Report - F-Secure [Infographic] | E-Learning-Inclusivo (Mashup) | Scoop.it](https://img.scoop.it/3WKggSg7n-Fjl4tKZAeUKDl72eJkfbmt4t8yenImKBVvK0kTmF0xjctABnaLJIm9)

















Um die Schüler auf die Arbeitsplätze von morgen optimal vorzubereiten, muss die Schule sich der modernen Informations- und Kommunikationstechnologien bedienen. Am Mittwoch stellte Bildungsminister Claude Meisch die Strategie "Digital (4) Education" vor, mit der die Schüler von heute, deren Lebenswirklichkeit bereits in weiten Teilen eine digitale ist, auf morgen vorbereitet werden sollen.
Um die Schüler auf die Arbeitsplätze von morgen optimal vorzubereiten, muss die Schule sich der modernen Informations- und Kommunikationstechnologien bedienen. Am Mittwoch stellte Bildungsminister Claude Meisch die Strategie "Digital (4) Education" vor, mit der die Schüler von heute, deren Lebenswirklichkeit bereits in weiten Teilen eine digitale ist, auf morgen vorbereitet werden sollen.